by Gerald McQuaid and Domenico Raffaele Cione
Imminently, the Directive 2014/41/EU of the European Parliament and of the Council of 3 April 2014 regarding the European Investigation Order (EIO) in criminal matters [1] is expected to become part of the EU-nations’ national laws. This EU directive requires each European Member State to transpose the directive into national law by 22 May 2017 (Article 33). This EIO describes the possibilities about lawful interception (LI) of telecommunications and collection of traffic and location retained data (RD) extended to network scenarios out of a pure national network context: an EIO may be issued for the interception of telecommunications by a Member State to obtain intercepted data of a target when using a communication service in a CSP’s network located in another Member State country (ref. Article 30 of [1]).
From the second quarter of 2016, ETSI TC LI has started to study different LI/RD Architecture reference models to address the new EIO requirements which imply that an LEA of a country (country B) will be able to get intercepted data of a target using a communication service in a CSP network located in another country (country A) in certain circumstances. Following different technical evaluations, ETSI TC LI agreed to support such data transfer between different national borders at the LEA’s domain level without impacting the CSP interception domain implementation. They were introduced the concepts of Requesting Authorized Authority (reqAA) and Responding Authorized Authority (resAA) with the corresponding Monitoring Facilities reqLEMF (in reqLEA) and resLEMF (in resLEA).
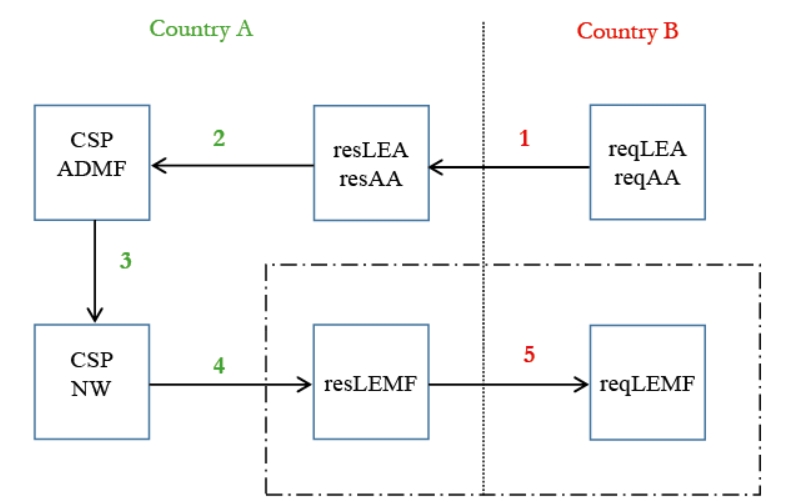
The new ETSI Architecture standard model for EIO is shown in Figure 1 which introduces five different interfaces steps:
- The requesting LEA or AA sends a message to responding LEA or AA specifying the data it needs.
- If accepted the responding LEA or AA forwards this request to the CSP. HI1 standard defined by [2] may be used for such order towards the administrative entity of the CSP where the target is requested to be intercepted.
- The CSP activates the request as a pure national request.
- The CSP provides the intercepted data IRI and CC or RD to the responding LEMF by using the already available and standardized HIs (i.e. IP delivery HIs based on TS 102 232 parts mechanism, ref. [3])
- The responding LEMF sends data forward as IRI IW and CC IW or RD IW data in (near) real time to the requesting LEMF.
ETSI TC LI is working to define this latter step 5 interface by writing a new Technical Specification for Inter LEMF Handover Interface, ref. [4]. This work has significant support in ETSI by all members types (Government, Network operators, MF/DF system providers) and it is planned to be finalized by mid 2017 to allow its implementation in several European countries.
Figure 2 describes the functional diagram of this new HI which has been named “SMILE” from SMART [HANDOVER] Interface [BETWEEN] LEAs. ETSI TC LI approach is defining HI-S based on re-using existing standard HIs, e.g. HI-S for LI refers to TS 102 232 part 1 to 7 [3] and HI-S for RD refers to TS 102 657 [5]. For the network layer, HI-S is proposed to use public Internet IP-VPN interconnection of the involved LEMFs or network connection secured by other means. As with other standard HIs, HI-S has been structured to manage two different data flows in term of IRI and CC by defining distinctive transmission interface paths, HI-2S and HI-3S, as specified by figure 3.
As of today, ETSI TC LI is working on a specification [4] for architecture elements definition and requirements setting (e.g. general, legal, functional requirements) and has planned to work in the first quarter of 2017 to address the other relevant aspects of security, correlation, identity handling, transport/application layers detailing. When published, the TS [4] will represent the first ETSI TC LI specification defining a technical interface in the LEA domain, e.g. outside of the pure CSP domain, but mostly based on the reuse of implementations provided by CSPs. The resulting standard will result in greater efficiency and reduced impact on all parties concerned. ©
ABBREVIATIONS
AA Authorized Authority
CC Content of Communication
CSP Communication Service Provider
EIO European Investigation Order
HI Handover Interface
IRI Intercept Related Information
IW Interworking
LEA Law Enforcement Agency
LEMF Law Enforcement Monitoring Facility
LI Lawful Interception
RD Retained Data
reqAA Requesting Authorized Authority
reqLEMF Requesting LEMF
resAA Responding Authorized Authority
resLEMF Responding LEMF
REFERENCES
[1] Directive 2014/41/EU of the European Parliament and of the Council of 3 April 2014 on the European Investigation Order in criminal matters. [EN] http://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX:32014L0041 [IT] http://eur-lex.europa.eu/legal-content/IT/TXT/?uri=CELEX:32014L0041
[2] ETSI TS 103 120 Lawful Interception (LI); Interface for warrant information v1.1.1 (2016-01)
[3] ETSI TS 102 232-1 & -2, -3, -4, -5, -6, -7 Lawful Interception (LI); Handover Interface and Service-Specific Details (SSD) for IP delivery; Part 1, 2, 3, 4, 5, 6, 7.
[4] draft ETSI TS 103 462 Lawful Interception (LI); Inter LEMF Handover Interface v0.0.2 (2016-11)
[5] ETSI TS 102 657 Lawful Interception (LI); Retained data handling; Handover interface for the request and delivery of retained data v1.17.1 (2015-12).












